
Atlant Security’s SMB cyber security consulting services help small business customers succeed in a resource-constrained, extremely competitive world. We have helped solopreneurs, small law firms, and commodity trading companies. The list of our customers also includes banks, government organizations, and software development companies. You can rely on the high-quality consulting of our team of experts, who have vast global cybersecurity consulting experience.
Imagine: you gain access to the minds and experience of the best cyber security experts in the world. The ones employed by Amazon, Microsoft, and Google – but they work for YOU!
Now imagine the difference between working with them versus working with your local talent or the solution providers you have worked with until now.
After each successful project, the results-oriented attitude, the speed of solving your challenges, and professional documentation are given to you.
This is the difference between owning a 10-year-old car and flying in a private jet.
Our mission is to make our customers feel every interaction with us, like flying in a private jet. No hassle, just fast and mind-blowing results.
If your small business needs cyber security consulting services, why settle with a local low-quality provider when you can have the best experts in the world?
Best of all? If you have just a few employees / computers, all of the 14 defense areas will be covered in just a few weeks!
💡 You can then go to your own potential clients and win new business by showing how well you can protect your clients’ data!
We will help you establish secure access management, prevent password reuse and eliminate easy-to-guess passwords. You will know who has access to what and why, at any time! We can also get you to passwordless authentication!
We check for mitigation controls for 17 types of cyber attacks: account compromise, unauthorized access, ransomware, network intrusions, malware infections, sabotage, security policy violations, etc.
Everyone in your company will receive appropriate security awareness training for their role. And people will remember what it was about! In the end, we will test the effectiveness of the training with phishing simulations.
Microsoft 365 has 280+ security settings. Amazon Web Services and Azure have hundreds of security configuration options, too - we will take care of ALL of them!
We help our cybersecurity consulting for small business customers transform their IT infrastructure security by implementing Server & Network Device Hardening, Desktop Hardening, Network & Web Service security, Data Security, Backups, and much more.
How many vulnerable machines/apps can a company have in its network?
We help our customers establish and manage a Vulnerability management program which will gradually reduce the vulnerabilities in their network.
Getting access to a corporate account may grant a hacker access to all internal systems. We protect our customers by implementing secure authentication, ensuring the integrity and confidentiality of your communications.
Breach simulation is an integral part of every Information Security Program. Our customers can rely on us to support them in the initiation, execution and conclusion of a Penetration Test.
Software development should be a rapid, efficient and secure process. We help our customers integrate security into the design, development, testing, integration and deployment of their code.
Policies and Procedures are the governing laws even in a small company's business. The ones we create are living and breathing documents bringing order and structure to your security practices.
Secure Work From Home is one aspect of remote access, but we also take care of third party partners and outsourced employees, vendors, and guests.
This is exactly why we expand your defenses beyond VPN and add Zero-Trust as your main principle of defense.
Antivirus is just one of 12 controls we implement at small businesses to defend endpoints from advanced hacking attacks. These security controls prevent the exploitation via malicious documents, scripts.
You will be able to detect if any of your devices or applications were compromised in the past 24 hours.
Every Information Security Program we build for our clients is different. Your teams, infrastructure, applications and business objectives are different, and we often expand our services to serve your better.
Our team has been a part of the best cybersecurity consulting departments on this planet. Before founding Atlant Security, our founder, Alexander, was part of Microsoft’s security consulting team.
Cyber security experts from all over the world compete to get into Microsoft – and only the best get the opportunity to work there. The price for customers to work with Microsoft’s small business cyber security consulting team is then set extremely high – so we decided to change that.
You have the opportunity to work with the best at a very affordable price.
We achieve that by using the expertise of one stellar expert to serve several customers rather than utilizing them as a full-time employees at just one company.
By using the economies of scale principle, we give our customers the best without sacrificing anything.
“Our IT team takes care of cybersecurity.”
If we could have a dollar every time we heard that 🙂
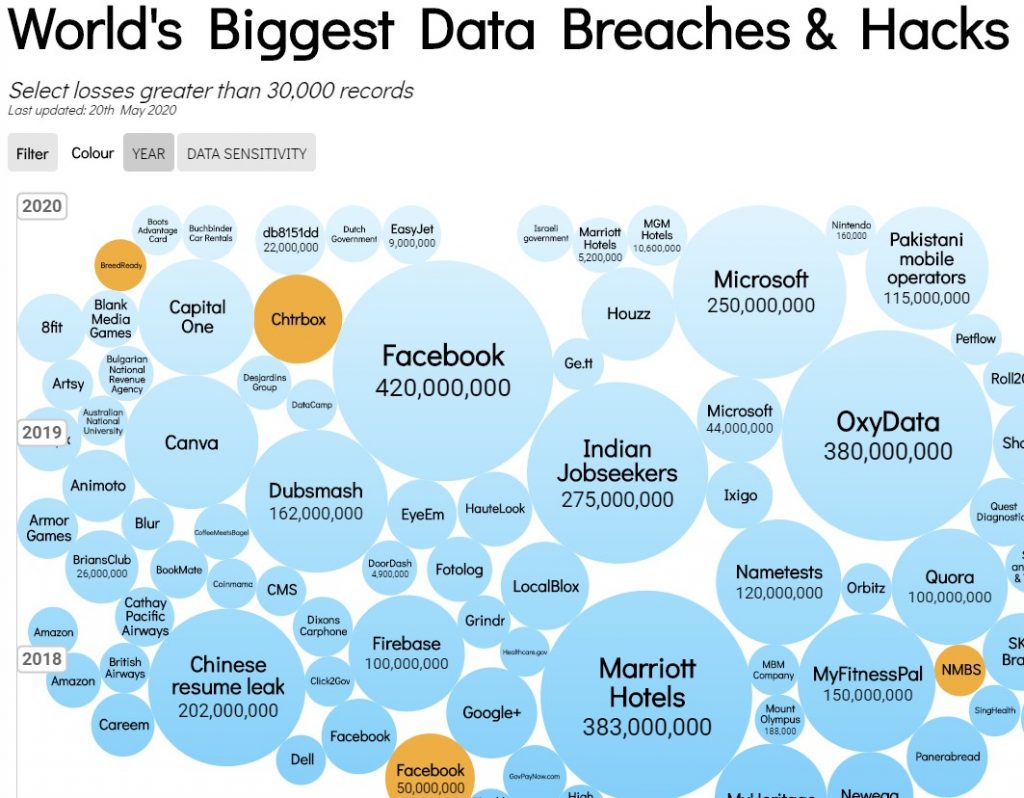
Just look at this graph. Every one of these companies had an IT team and every one of them firmly believed in their IT team’s ability to protect the company.
There is one problem with this belief: it is not based on facts. IT teams have very little experience in cybersecurity attack & defense methodologies. Their job is to build infrastructure and keep it running, much like every country has a construction industry.
But the construction industry can’t act as the military or the police – and if they did, the security of the country would suffer.
We believe this is what happens usually before a company gets hacked – their IT department is given the responsibility of defense. It inevitably leads to a security breach. In 100% of the cases.
When small business employees create passwords, they usually reuse one of their existing passwords or patterns.
This is extremely risky!
All a hacker needs to do to hack your emails in that case would be to find that particular employee’s password on any of the websites they’ve used. If that site was hacked in the past, all passwords of all its users become public and known to the hackers.
In that case, if they use the same password for their corporate email account, your company’s security will be compromised!
Through our SMB cyber security consulting services we help our customers establish a secure password & access management practice.
Small & medium business experience 17 types of cybersecurity attacks on a regular basis.
IT departments are normally aware of 3 or at most 4 of them – phishing (stealing credentials through fake login forms and pages), malware, password guessing (bruteforce) and DDoS (Distributed Denial of Service).
And even when they are aware of them, they usually don’t know how to mitigate them properly.
This is why we see so many small businesses getting hacked!
Our SMB cybersecurity consulting services are designed to help you mitigate all 17 types of cyberattacks.
Making your team aware of cyber threats and hacking methods is crucial to ensuring the safety of your company.
The market is flooded with cybersecurity awareness training services and companies.
Should you just pick one and try it?
What if it is not effective and how do you make security awareness training effective?
Save money and time and let our small business cybersecurity consulting team help you. We have helped many small businesses like yours run successful security awareness programs and can help, you, too!
Cybersecurity consulting is a service provided by cybersecurity experts to help organizations better protect their digital assets from various cyber threats. Consultants analyze the current security status, identify vulnerabilities, create strategies for risk mitigation, and implement security measures.
Any organization that uses digital systems – from small businesses to multinational corporations and government agencies – can benefit from cybersecurity consulting services. It’s especially important if you’re handling sensitive data like financial information or personal client details.
A cybersecurity consultant carries out various tasks, including risk assessments, designing security protocols, training employees on safe practices, and managing data breach incidents. They work closely with the organization to develop a comprehensive security strategy tailored to their needs.
Cybersecurity consultants use their expertise to identify potential vulnerabilities in your systems and recommend necessary changes. They can help you develop a robust security strategy, educate your employees on best practices, and ensure your company is compliant with relevant regulations, thus reducing the risk of costly data breaches.
Cybersecurity consulting can protect against a variety of threats, such as malware, phishing scams, denial-of-service attacks, and ransomware. Consultants also help secure your systems from insider threats and ensure your digital assets are safe even as cyber threats evolve.
Prevention is often cheaper than cure. Investing in cybersecurity consulting services can save your organization from the financial losses associated with data breaches, which include, but are not limited to, regulatory fines, legal fees, and reputational damage.
While having an in-house team can be beneficial, it’s not always practical, especially for smaller organizations. Cybersecurity consultants can provide expertise and resources that might be unaffordable or unnecessary on a full-time basis. They can also bring an outsider’s perspective to identify overlooked vulnerabilities.
The process often starts with a thorough assessment of your current cybersecurity state. From there, the consultant will provide recommendations, help implement changes, and monitor progress. This process is often cyclical, as cybersecurity is an ongoing effort requiring constant updates and revisions.
Regular consultations are recommended since cyber threats are continually evolving. Many organizations opt for yearly audits at a minimum, with some preferring more frequent check-ins. It will depend on your organization’s size, the nature of your data, and your industry’s regulations.
Absolutely. Cybersecurity consultants are well-versed in various regulations, such as the General Data Protection Regulation (GDPR) or the California Consumer Privacy Act (CCPA). They can help ensure that your organization’s cybersecurity practices meet these requirements, avoiding potential legal issues.
Atlant Security © 2023. All rights reserved