SOC 2 Type 1 vs. Type 2: The Ultimate Guide for Startups, CTOs & Compliance Leads
Alexander Sverdlov
Security Analyst

Why This Comparison Matters
Every startup eventually hits a wall: a major client says, "We need your SOC 2 report."
But which one? Type 1 or Type 2?
Making the wrong choice can:
-
Cost you $30K+ in wasted time
-
Delay enterprise deals by 3–6 months
-
Force you into a second audit before year-end
This guide gives you the full breakdown.
We'll cover:
-
🧠 The technical differences between Type 1 and II
-
⏳ How long each audit really takes
-
💼 Which one your customer actually cares about
-
💰 The cost breakdown (including hidden costs)
-
🔁 How to move from Type 1 → Type 2 the smart way
-
⚙️ Tools that automate the grind
-
📅 A full audit calendar with real deliverables
-
🧠 Buyer psychology and procurement insights
-
✅ GRC platform and auditor selection
What Is SOC 2, Really?
SOC 2 (System and Organization Controls 2) is an audit framework governed by the AICPA. It exists to help your customers understand one thing:
"Can we trust you with our data?"
SOC 2 audits look at how your company meets the five Trust Services Criteria:
| Trust Services Criterion | Description |
|---|---|
| 🔐 Security | The only required category. Firewalls, access controls, patching, and backups. |
| ☁️ Availability | Can your systems deliver uptime? Is monitoring in place? |
| ✅ Processing Integrity | Do your systems do what you promise, accurately and reliably? |
| 🙈 Confidentiality | Can you keep sensitive data away from the wrong people? |
| 🔏 Privacy | Are you following data collection and handling commitments? |
Most startups begin with Security only. You add the others later, depending on industry and customer requirements.
📎 You don't "get certified" in SOC 2 - you get an attestation report from a licensed CPA firm.
In the next section (Part 2), we'll break down what a SOC 2 Type 1 really is - when to choose it, what it proves, and why it may be a great (or poor) strategic fit.
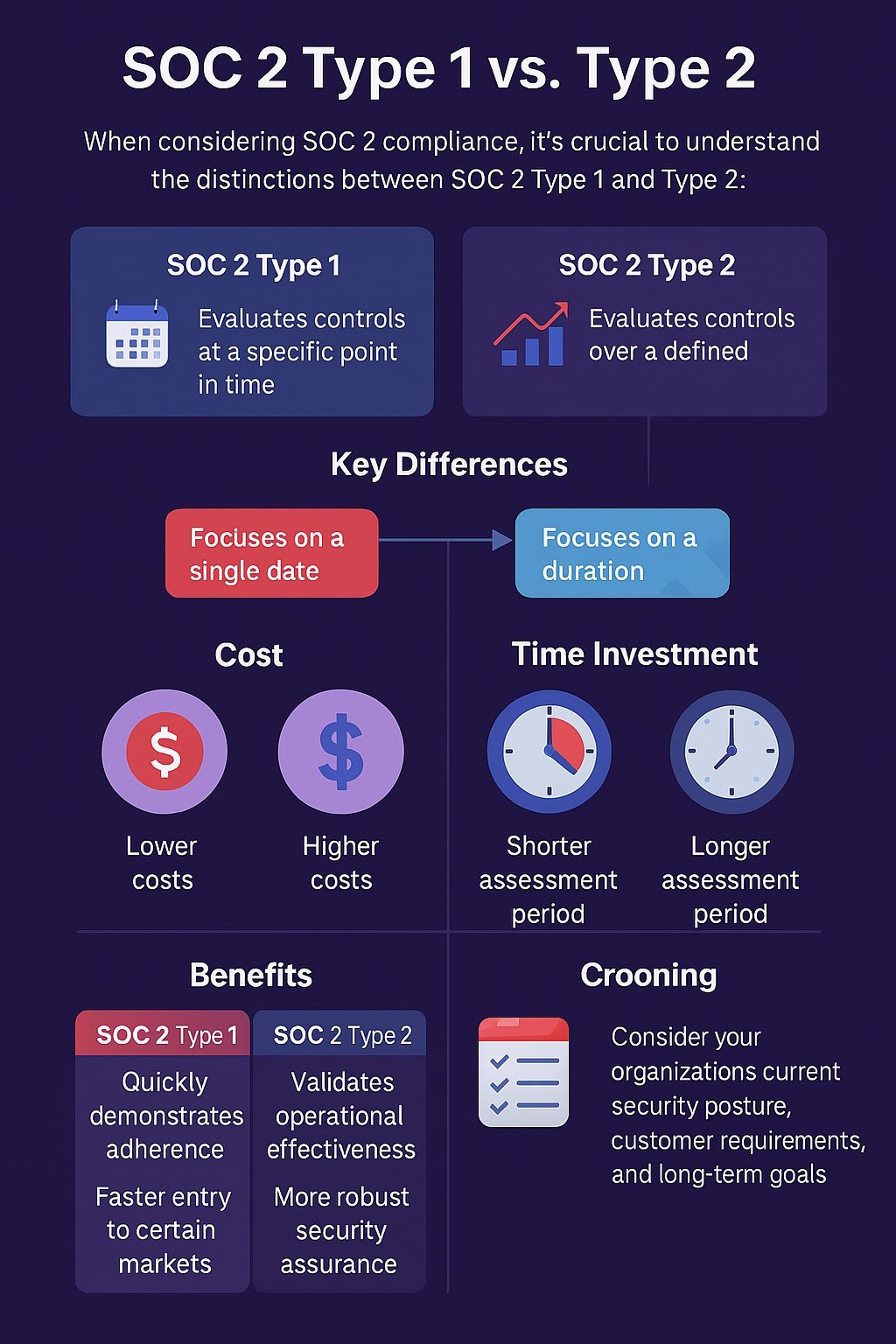
SOC 2 Type 1 is your first step into the world of trust. But it's not a badge of long-term reliability. It's a snapshot - a declaration that on a specific day, your company had the right policies and controls in place.
✅ What It Proves
SOC 2 Type 1 answers this question:
"Have you designed and documented the necessary controls to protect customer data?"
It typically covers:
-
📄 Written security policies (acceptable use, incident response, access control)
-
🔐 Technical implementations (MFA, encryption, audit logging)
-
🧑💼 HR procedures (background checks, security awareness training)
-
🖥️ Infrastructure documentation (architecture diagrams, cloud setup)
🔍 Example Tools Auditors Will Look For
| Control Area | Evidence You Might Submit |
| MFA | Screenshot of enforcement via Okta or Google Workspace |
| Security Training | CSV export from KnowBe4 or Drata LMS |
| Policy Acknowledgement | Signed PDFs or DocuSign records |
| Asset Inventory | Export from Jamf, Kandji, or Intune |
The audit is point-in-time. If your audit date is March 1, that's the only day the auditor cares about. If your system fails on March 2? Not in scope.
🚫 What It Doesn't Prove
Type 1 does not show:
-
That your team follows policies consistently
-
That your controls work under pressure (e.g., incidents)
-
That you complete recurring tasks like access reviews or patching
-
That you're audit-ready month after month
🧠 Type 1 = design review, not operational proof.
✅ When SOC 2 Type 1 Makes Sense
| Scenario | Why Type 1 Works |
| Seed/Series A stage | Need fast trust signal for early traction |
| < $100k ARR deals | Smaller buyers may accept it |
| Product evolving quickly | Controls may change before next audit |
| Investor due diligence | Helpful for building confidence |
❌ When Type 1 Falls Short
| Scenario | Why It Won't Cut It |
| > $250k contracts | Procurement will want repeatable proof |
| Working with banks or hospitals | Regulated clients require operational assurance |
| RFPs ask for "security operations evidence" | You'll need logs, not just policies |
| Facing competition | Others may already have Type 2 |
🔁 Type 1 is often a temporary bridge to Type 2.
SOC 2 Type 2 is the gold standard for operational security maturity.
Unlike Type 1, which shows your controls exist, Type 2 proves you actually use them. It's the difference between showing gym membership paperwork... and showing you've worked out every week for six months.
📌 What SOC 2 Type 2 Proves
Type 2 demonstrates that your controls are:
-
✅ Implemented
-
✅ Maintained
-
✅ Reviewed
-
✅ Working
Across an audit window - typically 3, 6, or 12 months.
🧾 What Auditors Want to See
| Control | Evidence Required |
| MFA Enforced | Auth logs from Okta, Google Workspace |
| Access Reviews | Quarterly review logs, Jira tickets, sign-offs |
| Patch Management | Monthly vulnerability scans, change control logs |
| Incident Response | IR plan, drill logs, post-mortem documentation |
| Backup Testing | Screenshots from test restore + recovery RTO logs |
💡 Auditors expect timestamps and recurrence - not just a single screenshot.
🧠 Why Buyers Trust Type 2
Buyers, especially in finance, healthcare, and legal tech, are trained to look for:
-
Proof of control execution
-
Evidence of operational security
-
Gaps closed proactively
When you share a Type 2 under NDA, it:
-
✅ Speeds up vendor security reviews
-
✅ Reduces the size of InfoSec questionnaires
-
✅ Gives confidence to procurement and legal
-
✅ Helps your sales team avoid friction
💬 Quote from a Buyer
"We treat Type 1 as a nice try. But if you want to close with us, bring a Type 2 or don't bother." - Procurement Lead, US Healthcare SaaS
📊 When Type 2 Is a Competitive Advantage
| Scenario | Buyer Response Without Type 2 | With Type 2 |
| $500k+ contract | Delays, follow-ups, risk flags | Shortlist fast-track |
| Security questionnaire | Dozens of control questions | 70% skipped with attached report |
| RFPs from banks | Soft disqualification | Point-scoring asset |
| VC diligence (Series B+) | Additional questions | Risk factor cleared |
🛡️ A Type 2 report becomes a revenue multiplier once you cross $1M ARR or hit enterprise sales.
SOC 2 audits aren't cheap. But it's not just the price tag that hurts - it's the hidden time, tools, and distractions that hit your engineering, legal, and leadership teams.
Let's break down what Type 1 and Type 2 actually cost.
💵 SOC 2 Cost Breakdown
| Category | Type 1 Estimate | Type 2 Estimate |
| GRC Platform (Vanta, Drata, etc.) | $7,000 – $25,000 | $7,000 – $25,000 |
| Auditor Fee | $10,000 – $25,000 | $25,000 – $60,000 |
| Internal Hours (team time) | 80–150 hrs | 200–400 hrs |
| External Consultant | Optional, $5,000–$15,000 | Optional, $10,000–$25,000 |
| Lost Sales Time | Up to $50,000 in delayed deals | Up to $150,000 in extended cycles |
🧠 Many founders overlook the opportunity cost of team focus and time spent chasing evidence manually.
⏱️ Audit Timeline: What to Expect
Type 1 Timeline
-
📅 1–2 weeks: Readiness assessment
-
⚙️ 3–4 weeks: Control implementation
-
📝 1–2 weeks: Documentation
-
🔍 2 weeks: Fieldwork & evidence collection
-
✅ 1–2 weeks: Final report delivery
🕓 Total: ~8–10 weeks (faster if well prepared)
Type 2 Timeline
-
📅 1–2 weeks: Readiness + GRC platform setup
-
🔁 3–12 months: Observation period
-
🧾 2–4 weeks: Evidence submission
-
👨⚖️ 2–4 weeks: Auditor review
🕐 Total: 6–14 months (depending on monitoring window)
⚠️ Hidden Pitfalls That Stall SOC 2
| Risk | Description | Impact |
| ❌ Incomplete policy acknowledgments | Employees haven't signed your policies | Audit failure or delay |
| ❌ No access review logs | You didn't review or document access rights | Fails critical control |
| ❌ No backup test logs | Backups exist but aren't tested | Raises red flags for availability |
| ❌ Rushed vendor selection | Cheap auditors can delay reporting or fail you | Wasted months and $$ |
| ❌ Outdated infrastructure | AWS S3 buckets are public, no MFA on root | Rework + audit remediation |
📋 Real-World Hidden Tasks
Even with a GRC tool, you'll need to:
-
🧩 Track offboarding tickets in Jira or equivalent
-
🧠 Schedule security awareness training and prove completion
-
🔐 Enforce MFA across all accounts, not just production
-
📁 Store evidence in a clean, auditable way
-
📢 Train your team to respond to auditor questions correctly
If you've passed SOC 2 Type 1, congratulations. But don't celebrate too long - most of your buyers will still ask for Type 2.
Here's how to move forward without wasting time or repeating work.
🛣️ Your 6-Step Transition Plan
1. 📋 Review Your Type 1 Findings
Your auditor probably gave you observations or minor gaps. Fix them - Type 2 will check those same controls in action.
2. 📅 Choose Your Observation Period Wisely
| Period | Pros | Cons |
| 3 Months | Fast proof, good for urgency | Less robust, may not satisfy big buyers |
| 6 Months | Startup-friendly standard | Moderate evidence volume |
| 12 Months | Strongest buyer trust | Longest time to wait for a report |
🧠 Many SaaS startups begin with 6 months for speed + credibility.
3. 🔁 Automate Evidence Collection
You'll need:
-
Rolling access review records
-
Recurring training logs
-
System logs from firewalls, SSO, backups
-
Change management tickets
Platforms like Drata, Vanta, and Secureframe help - but they won't do the thinking for you.
4. 📊 Run Internal Checkpoints Every Month
Make sure:
-
✅ Everyone completes onboarding tasks
-
✅ Patching is documented
-
✅ All access changes are logged
-
✅ New vendors are risk assessed
Tip: Create a "SOC 2 Calendar" with monthly, quarterly, and annual tasks for your DevOps, HR, and Security teams.
5. 👨⚖️ Schedule Fieldwork in Advance
Fieldwork = the official audit window.
-
Set dates 30+ days in advance
-
Prepare your team to answer questions
-
Preload documents and logs for the auditor
6. 📄 Prepare for Report Delivery
Your Type 2 report will include:
-
Management assertion
-
Auditor opinion
-
Control list with test results (passed/failed)
-
Description of systems and infrastructure
✅ Deliver it under NDA and include it in vendor security review packages.
f you've passed SOC 2 Type 1, congratulations. But don't celebrate too long - most of your buyers will still ask for Type 2.
Here's how to move forward without wasting time or repeating work.
🛣️ Your 6-Step Transition Plan
1. 📋 Review Your Type 1 Findings
Your auditor probably gave you observations or minor gaps. Fix them - Type 2 will check those same controls in action.
2. 📅 Choose Your Observation Period Wisely
| Period | Pros | Cons |
| 3 Months | Fast proof, good for urgency | Less robust, may not satisfy big buyers |
| 6 Months | Startup-friendly standard | Moderate evidence volume |
| 12 Months | Strongest buyer trust | Longest time to wait for a report |
🧠 Many SaaS startups begin with 6 months for speed + credibility.
3. 🔁 Automate Evidence Collection
You'll need:
-
Rolling access review records
-
Recurring training logs
-
System logs from firewalls, SSO, backups
-
Change management tickets
Platforms like Drata, Vanta, and Secureframe help - but they won't do the thinking for you.
4. 📊 Run Internal Checkpoints Every Month
Make sure:
-
✅ Everyone completes onboarding tasks
-
✅ Patching is documented
-
✅ All access changes are logged
-
✅ New vendors are risk assessed
Tip: Create a "SOC 2 Calendar" with monthly, quarterly, and annual tasks for your DevOps, HR, and Security teams.
5. 👨⚖️ Schedule Fieldwork in Advance
Fieldwork = the official audit window.
-
Set dates 30+ days in advance
-
Prepare your team to answer questions
-
Preload documents and logs for the auditor
6. 📄 Prepare for Report Delivery
Your Type 2 report will include:
-
Management assertion
-
Auditor opinion
-
Control list with test results (passed/failed)
-
Description of systems and infrastructure
✅ Deliver it under NDA and include it in vendor security review packages.
You can't brute-force a SOC 2 Type 2 audit - not without wasting time and burning out your team. The best security teams automate wisely and use the right tech stack to collect, track, and prove compliance.
🧰 Must-Have Tools for SOC 2 Compliance
| Tool Category | Examples | Why It Matters |
| 🧩 GRC Platforms | Vanta, Drata, Secureframe | Automate evidence collection, assign controls, track policies |
| 🧑💼 HRIS | Rippling, BambooHR | Automate onboarding/offboarding, map users to policies |
| 🔐 Identity & Access | Okta, Google Workspace, Azure AD | MFA, SSO, audit logs, user management |
| 🔍 Monitoring & Logging | Panther, Datadog, AWS CloudTrail | Collect logs, show alerting, detect changes |
| 📁 Document Management | Notion, Confluence, Dropbox | Policy versioning, acknowledgments |
⚡ Your GRC tool is the hub - but you still need strong integrations and team accountability.
🧩 Control Evidence Examples
| Control Area | Evidence You'll Need |
| Access Management | Monthly/quarterly access review reports signed by manager |
| Vendor Management | Risk questionnaires, DPAs, SOC reports, contract dates |
| Backup & Recovery | Backup job logs, restore drill screenshots, RTO measurement |
| Incident Response | Tabletop simulation calendar, reports, Jira tickets |
| Change Management | GitHub PRs, JIRA change tickets, approval workflows |
🧠 Policy Template Starter Pack
Don't write your policies from scratch. Use vetted templates:
-
📃 Acceptable Use Policy
-
🔐 Access Control Policy
-
💾 Backup & Recovery Policy
-
🧑🏫 Security Awareness & Training
-
🚨 Incident Response Policy
-
🧮 Risk Assessment Policy
👉 You can get these from:
💡 Pro Tips to Cut Audit Pain
-
⏰ Use calendar automation for recurring tasks (e.g., Google Calendar reminders)
-
🧪 Simulate audits quarterly so nothing piles up
-
🧠 Train your team to answer auditors confidently (avoid "I'm not sure")
-
📥 Centralize logs and backups so no one digs around Slack mid-audit
Once you've achieved SOC 2 compliance - especially Type 2 - don't hide it. But also: don't overpromise or misrepresent it.
🧠 Understand What You Can and Can't Say
| You Can Say | You Can't Say |
| ✅ "We've completed a SOC 2 Type 2 audit." | ❌ "We are certified SOC 2" (SOC 2 is not a certification) |
| ✅ "Report available under NDA" | ❌ "We passed all controls" (auditors don't use that phrasing) |
| ✅ "Audited by a licensed CPA firm" | ❌ "We're immune to security breaches" |
📌 Use the word "attestation" - not "certification."
🧾 Where to Communicate It
🔒 1. Security Page on Your Website
Include:
-
A short paragraph on your SOC 2 journey
-
Which Type you achieved (I or II)
-
A CTA like: "Request our report under NDA"
🧑💼 2. Sales Enablement Docs
Give your team:
-
A 1-pager explaining what SOC 2 is
-
Common buyer objections & answers
-
NDA flow to access your report
💌 3. Fundraising & Investor Updates
Show:
-
A timeline of your compliance effort
-
How SOC 2 impacted your pipeline or customer trust
-
Future plans (e.g. ISO 27001, HIPAA)
📣 4. LinkedIn or Blog Announcements
Sample post:
We've completed our SOC 2 Type 2 audit! This strengthens our commitment to security and trust. Thanks to our team, partners, and customers who made this possible.
📊 5. RFP Responses & Vendor Portals
Language to use:
We've undergone a SOC 2 Type 2 audit conducted by [Auditor Firm], covering a [6/12]-month period, available under NDA. Controls include access reviews, incident response testing, vendor management, and encryption protocols.
🚩 What Not to Do
-
❌ Don't link to the full report publicly
-
❌ Don't reuse it for unrelated customers (some clients will want a custom assessment)
-
❌ Don't assume SOC 2 solves all buyer concerns - it's a trust accelerator, not a substitute for solid architecture
Want help preparing your security site, SOC 2 Q&A playbook, or investor materials? Let's make trust your fastest growth lever.
See also: Cybersecurity Companies in Riyadh: The 2025 Expert Guide to Choosing the Right Partner

Alexander Sverdlov
Founder of Atlant Security. Author of 2 information security books, cybersecurity speaker at the largest cybersecurity conferences in Asia and a United Nations conference panelist. Former Microsoft security consulting team member, external cybersecurity consultant at the Emirates Nuclear Energy Corporation.