DORA checklist to speed up your compliance
Alexander Sverdlov
Security Analyst

✅ DORA COMPLIANCE CHECKLIST
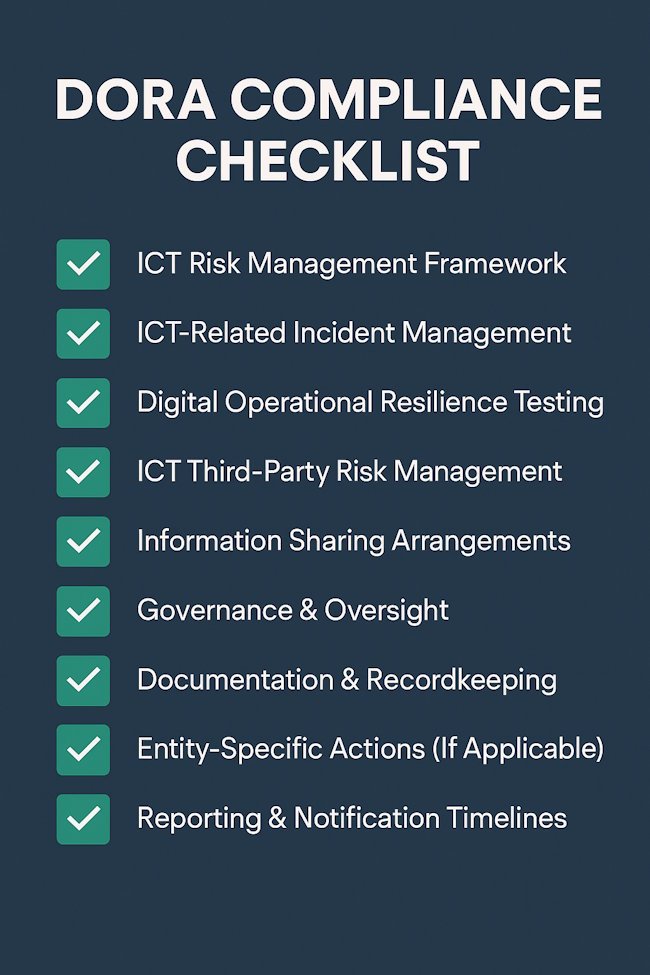
1. ICT RISK MANAGEMENT FRAMEWORK
-
Define roles and responsibilities for ICT risk (board, management, ICT, etc.)
-
Integrate ICT risk into your overall enterprise risk management
-
Maintain an up-to-date ICT risk register
-
Classify ICT systems based on criticality and business impact
-
Document all ICT assets, dependencies, and interconnections
-
Establish security baselines for systems and networks
-
Maintain secure software development practices
-
Document change management procedures for all ICT components
-
Implement patch management with defined timelines
-
Continuously monitor ICT threats and vulnerabilities
2. ICT-RELATED INCIDENT MANAGEMENT
-
Define and classify ICT incidents (major, significant, minor)
-
Establish an ICT incident response plan
-
Implement 24/7 monitoring and detection capabilities
-
Record all ICT incidents in a centralized logbook
-
Conduct root cause analysis for major incidents
-
Notify regulators (e.g., national competent authority) within 4 hours of classifying a major incident
-
Communicate incidents to impacted customers or partners where relevant
-
Analyze trends and metrics to improve resilience
3. DIGITAL OPERATIONAL RESILIENCE TESTING
-
Develop a risk-based testing program (annual minimum)
-
Conduct vulnerability assessments and penetration testing
-
Test backup restoration processes regularly
-
Test incident response plans (tabletop and live exercises)
-
Carry out scenario-based testing for critical services
-
Conduct Threat-Led Penetration Testing (TLPT) at least every 3 years for critical ICT
-
Document test results and remedial actions
-
Report material gaps and mitigation plans to senior management
4. ICT THIRD-PARTY RISK MANAGEMENT
-
Maintain a register of all ICT third-party service providers
-
Categorize providers based on criticality
-
Assess and document third-party risks before onboarding
-
Ensure all contracts include:
-
Service levels and performance targets
-
Access rights for audits and inspections
-
Data security and location of processing
-
Exit and termination clauses
-
-
Monitor third-party performance and compliance continuously
-
Establish a third-party incident notification process
-
Ensure right to terminate in case of systemic risk or regulatory breach
-
Perform due diligence for fourth-party risks
5. INFORMATION SHARING ARRANGEMENTS
-
Participate in trusted information sharing groups (ISACs, NIS cooperation groups, etc.)
-
Define internal rules for how threat intel is shared internally and externally
-
Use shared intelligence to update risk models and detection capabilities
-
Ensure all information sharing complies with GDPR and competition law
6. GOVERNANCE & OVERSIGHT
-
Assign ultimate ICT risk responsibility to the board of directors
-
Review ICT risk and resilience metrics in regular board meetings
-
Ensure senior management oversees compliance with DORA
-
Conduct internal audits of ICT risk, incidents, and resilience
-
Train staff on DORA obligations and operational resilience
-
Include DORA compliance in annual internal control reports
7. DOCUMENTATION & RECORDKEEPING
-
Maintain all relevant policies, procedures, and registers:
-
ICT risk management framework
-
Incident response and notification logs
-
Testing reports and remediation
-
Third-party contracts and assessments
-
-
Store records securely and make them available to regulators upon request
-
Keep documentation updated and reflect changes in organizational structure or ICT setup
8. ENTITY-SPECIFIC ACTIONS (IF APPLICABLE)
For critical or important ICT third-party service providers:
-
Prepare for potential designation by the European Supervisory Authorities (ESA)
-
Ensure readiness for direct oversight by the ESAs
-
Cooperate with audits, reporting, and onsite inspections by regulators
9. REPORTING & NOTIFICATION TIMELINES
| Trigger | Deadline | Recipient |
|---|---|---|
| Major ICT Incident | Within 4 hours | National Competent Authority |
| Initial Impact Assessment | Within 1 business day | National Competent Authority |
| Final Report | Within 1 month | National Competent Authority |
| TLPT Results (if required) | On completion | National Competent Authority |
🔄 SUGGESTED REVIEW FREQUENCY
| Area | Review Frequency |
|---|---|
| ICT Risk Framework | Annually |
| Incident Response Plan | Semi-annually |
| Third-Party Risk Register | Quarterly |
| Resilience Testing Plan | Annually |
| Board Reporting | Quarterly |
| Staff Training | Annually |
| Policy and Documentation Updates | As needed |
You can download the whole Full_DORA_Compliance_Checklist
See also: Insider Threats in Cybersecurity: Identification, Prevention, and Mitigation Strategies

Alexander Sverdlov
Founder of Atlant Security. Author of 2 information security books, cybersecurity speaker at the largest cybersecurity conferences in Asia and a United Nations conference panelist. Former Microsoft security consulting team member, external cybersecurity consultant at the Emirates Nuclear Energy Corporation.