How to prevent SIM swap attacks
Alexander Sverdlov
Security Analyst

If you've been a victim of a SIM swap attack, a simple article is not what you need. You can read the post, of course, and you can prevent most future SIM swap attacks if you follow the advice listed here, but you should know this:
The people behind the attack are most likely not going to give up simply because you set a PIN on your activities at your cell provider. If you are under attack, reach out to us and let our experts build a digital fortress for you. We are constantly helping executives and high risk individuals protect their digital lives.
Now... let's get to some practical advice, in case you like doing things yourself!
🚨 SIM Swap Attacks Are Not Just Hacker Stunts - They're Precision-Engineered Heists
SIM swap attacks, also called SIM hijacking, are one of the most financially and psychologically devastating forms of digital theft. Unlike phishing or brute force attacks, SIM swaps are surgical: attackers bypass strong passwords, 2FA apps, and even encrypted email - all by hijacking a phone number.
Once your phone number is in the attacker's control, they can:
-
Intercept two-factor authentication codes (SMS 2FA)
-
Reset passwords to your email, bank, and crypto accounts
-
Impersonate you to your contacts or financial institutions
-
Lock you out of your digital life
And it only takes one call to your carrier.
Once an attacker controls your phone number, they follow a predictable - but devastating - path of account takeovers.
Here are the most commonly hijacked accounts, in order of risk, based on their ability to unlock other systems.
🧩 1. Email: The Master Key to Everything
📧 Why It's Targeted First
-
Password resets for almost every account go through your inbox.
-
Most people have recovery emails linked to their phone number.
-
Once your email is compromised, attackers can spoof you or reset everything else.
🔐 Common Attack Flow
-
Request password reset via SMS
-
Receive reset code on hijacked number
-
Change password
-
Delete alert emails to cover tracks
"Your Gmail is more important than your bank login. It resets your bank login."
- Alex Stamos, Former Facebook CISO
🏦 2. Bank Accounts & Investment Platforms
💰 What's at Risk
-
Wire transfers, Zelle/PayPal fraud
-
Changing contact details for identity theft
-
New credit card or loan applications
⚠️ How They Get In
-
Reset via SMS + email combo
-
Call customer support pretending to be you
-
Bypass knowledge-based verification (DOB, address, last four SSN)
Banks with weak identity verification procedures are frequent victims of social engineering abuse.
🔐 3. Crypto Exchanges & Wallets
🪙 Why They're High-Value
-
Instant liquidity
-
Irreversible transactions
-
No central fraud protection
🚨 Common SIM Swap Exploits
| Exchange | Known SIM swap breaches |
|---|---|
| Coinbase | 6,000+ users affected in 2021 (source) |
| Binance | Victims tricked with SMS OTP codes |
| Kraken | Targeted VIP accounts via number takeover |
In many cases, attackers swap SIMs, then log in simultaneously to email and exchange to pass 2FA challenges.
👥 4. Social Media Platforms
🎭 Why They Hijack Social Media
-
Run scams from verified accounts
-
Ask followers to send crypto
-
Damage your public image or brand
| Platform | Known Risks |
|---|---|
| Twitter/X | Hijacked via SMS reset or email compromise |
| Common impersonation tool for blackmail | |
| Used for BEC (Business Email Compromise) targeting vendors & execs | |
| Often linked to business ad accounts or payment methods |
🛍️ 5. Shopping & Delivery Apps
Attackers can:
-
Order products to drop sites
-
Steal saved credit cards
-
Change your shipping addresses
-
Access loyalty points and saved gift cards
Examples: Amazon, DoorDash, Uber, eBay
🧾 6. Government Portals & ID Services
Many services like:
-
IRS or tax filing portals
-
National health insurance websites
-
DMV accounts
…still use SMS verification or allow resets with basic PII + a phone number.
🧠 Part 3 Key Takeaway
Once an attacker has your number, they don't need to hack your password. They exploit recovery flows, customer service, and weak 2FA setups.
Your most valuable accounts are usually the easiest to access, because they're tightly linked to your phone number.
🎯 Who Do SIM Swappers Target?
While anyone can be a victim, high-net-worth individuals (HNWIs) and public-facing executives are top-tier targets. Why?
| Reason | Description |
|---|---|
| 💸 Large financial accounts | Crypto wallets, investment platforms, and offshore accounts are ideal targets |
| 🧠 Influence & Reputation | Attackers can impersonate the victim to damage brand or personal credibility |
| 🔐 Centralized control | One phone number often unlocks everything - email, banking, business accounts |
| 📱 Social visibility | Public profiles make it easy to gather personal information used in attacks |
"SIM swaps aren't random. They're deliberate, researched, and aimed at the most valuable targets."
- Eva Galperin, EFF Director of Cybersecurity
🧨 Real-World Examples: When a Number Turns Into a Disaster
1. Michael Terpin - $24 Million Crypto Theft
In 2018, crypto investor Michael Terpin fell victim to a SIM swap. Using only his mobile number, hackers reset his email and then drained $24 million worth of cryptocurrency from his accounts. He later sued AT&T for gross negligence (Bloomberg).
2. Jack Dorsey - Twitter CEO's Account Hijacked
In 2019, Jack Dorsey's personal number was ported to another SIM. Attackers used it to hijack his Twitter account and post racist and offensive messages to millions of followers (NYT).
3. Joel Ortiz - The $5 Million Serial Swapper
At just 20 years old, Ortiz used SIM swaps to steal over $5 million in crypto from multiple victims. He targeted people at crypto events, tracked them online, and systematically drained their wallets. He was later sentenced to 10 years in prison (Wired).
📈 Why This Attack Works So Well
SIM swap attacks work because mobile carriers (like Verizon, T-Mobile, AT&T) are soft targets:
-
Support reps can be manipulated through social engineering
-
Porting a number often requires little more than a name, phone number, and one security question
-
Carriers often don't notify users of number transfers until it's too late
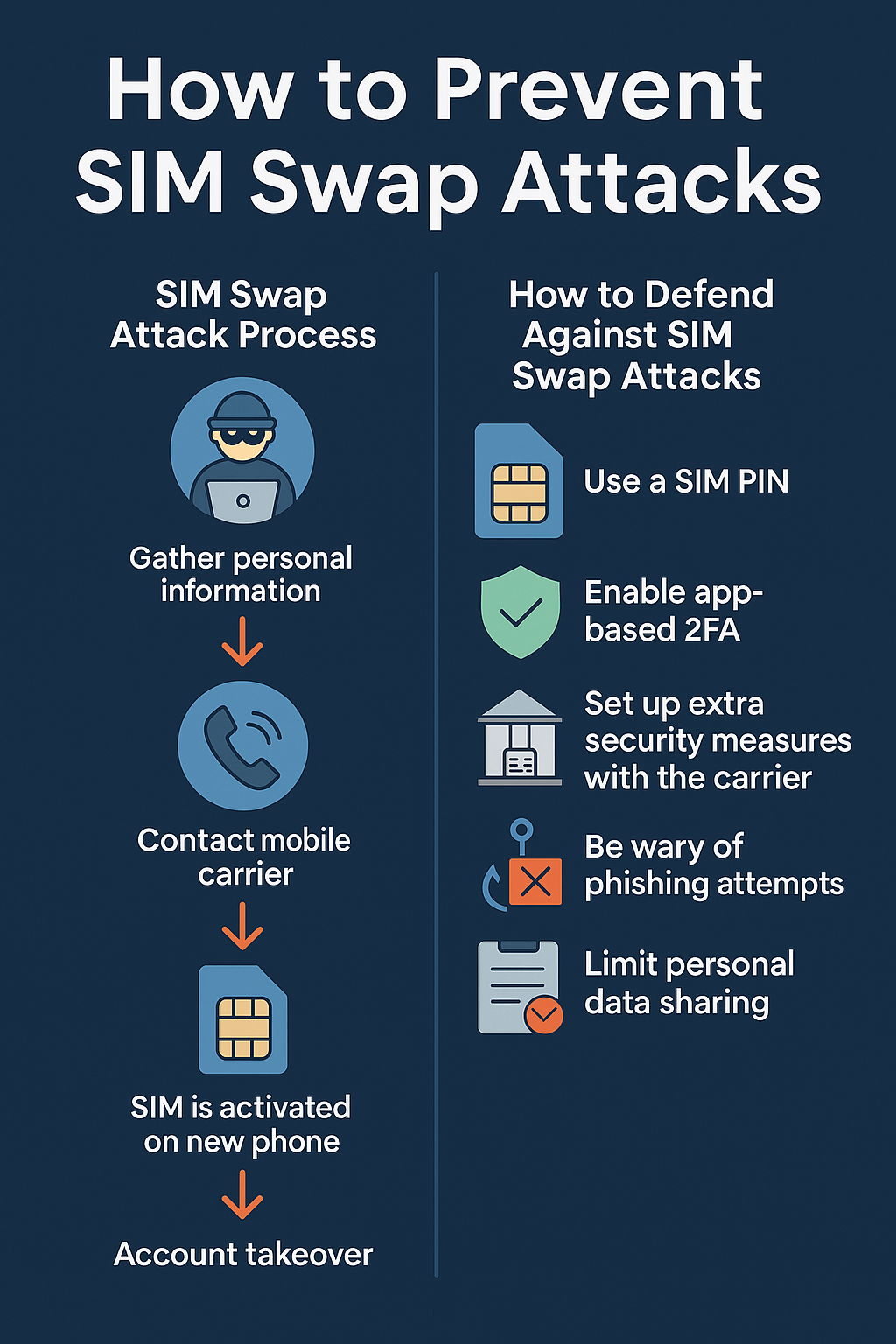
Figure 1. Five Things That Make SIM Swap Attacks Work.
Once the attacker controls the phone number, every account that uses SMS for verification is now theirs. Password resets. 2FA. New device logins. All routed through a number you no longer control.
❗ Consequences of a Successful SIM Swap
| Area | Impact |
|---|---|
| 💰 Financial Loss | Access to banking, crypto, and investment accounts |
| 📧 Identity Takeover | Reset email passwords, gain access to everything tied to email |
| 👨👩👧👦 Social Engineering | Impersonate you to your family, staff, or vendors |
| 📉 Business Fallout | CEO email hijacked, clients or partners scammed |
| 🕵️♂️ Doxxing | Full exposure of your private information |
| 🎭 Reputation Damage | Public-facing accounts defaced or used for scams |
🧠 Key Takeaway from Part 1
SIM swaps aren't just about your phone. They're about control.
Your number is the skeleton key to your digital world. If you're a high-net-worth individual or company executive, your phone number is your weakest link - and hackers know it.
SIM swap attacks require planning, coordination, and detailed victim knowledge. But they are shockingly easy to execute once attackers gather the right data.
Here's how these attacks typically unfold:
🧬 Step 1: Reconnaissance - Profiling the Target
Attackers begin by gathering Personal Identifiable Information (PII) about you. This can come from:
-
Data breaches (password dumps, account info)
-
Social media (birthdays, pet names, relatives, hometowns)
-
Data broker websites (Spokeo, PeopleFinder, Whitepages)
-
Old password reset questions (first school, mother's maiden name)
"People don't realize that oversharing online creates a blueprint for identity theft." - Rachel Tobac, Social Engineer & Hacker
🧾 Step 2: Social Engineering the Mobile Carrier
Using the info from Step 1, attackers call your mobile provider's customer service pretending to be you.
Common tactics:
-
Claiming the phone was lost or damaged
-
Providing fake documents like a driver's license (forged or AI-generated)
-
Offering matching address, SSN, and DOB info from breached databases
-
Using urgency or emotional manipulation: "I'm traveling and need my number restored!"
Some go further:
-
Bribing carrier employees directly
-
Using insider access through criminal marketplaces (e.g. SIM swap-as-a-service)
🔁 Step 3: SIM Porting (The Moment You Lose Control)
The attacker convinces the carrier to:
-
Port your number to a new SIM card (controlled by them)
-
Activate service on their device, killing service on yours
You will suddenly lose mobile signal. This is often the first sign a SIM swap has occurred.
🔓 Step 4: Taking Over Accounts
Now that they control your number, they go after everything you own. Examples:
| Account Type | What Happens |
|---|---|
| Email (Gmail, Outlook) | They request a password reset via SMS, take over your inbox |
| Crypto Exchange | They reset your login, drain your funds |
| Bank | With phone number + email, they pass verification and gain account access |
| Social Media | They request code to log in or reset password, then lock you out |
| Cloud Storage | Access backed-up docs, photos, ID scans |
🔥 Step 5: Lock You Out + Cover Tracks
The attacker will:
-
Change your email password
-
Enable 2FA with a new device they control
-
Remove your recovery options
-
In some cases, contact your bank or exchange pretending to be you
You may receive alerts like:
-
"Your phone number has been removed from your account"
-
"Your password has been changed"
-
"New device logged in from [location]"
By the time you see these alerts, it's often too late.
🧪 Case Study: Reddit SIM Swap Victim
"My number was ported. Within 5 minutes they got into my Gmail, then Coinbase, then drained $18K from my ETH wallet. T-Mobile said they couldn't do anything."
- Reddit user r/simswaphell
SIM swaps aren't random - they're targeted, planned, and fast. Once the attacker owns your number, they can cascade across your digital life in under an hour.
If you're a high-net-worth individual, security must be layered. Defending against SIM swaps requires combining carrier controls, hardware-based authentication, and identity compartmentalization.
Let's walk through exactly what to implement - step by step.
🔐 Step 1: Remove SMS-Based Two-Factor Authentication
SMS is the weakest form of 2FA. It's better than nothing - but not by much.
✅ Replace with:
| Account Type | Secure Alternative |
|---|---|
| YubiKey, Google Authenticator, Authy | |
| Crypto exchanges | Hardware wallet, TOTP app |
| Banking | App-based 2FA or biometric access |
| Social media | App-based codes or security key |
📌 Tools to Use:
-
YubiKey (best defense against phishing + SIM swap)
"YubiKeys are the gold standard of user authentication."
- Brian Krebs
📞 Step 2: Lock Down Your Carrier Account
Most SIM swaps exploit weak carrier policies. Here's how to harden yours:
🔐 U.S. Carrier Settings:
| Carrier | Defense Option |
|---|---|
| Verizon | Number Lock (MyVerizon app) |
| AT&T | Extra Security + Account Passcode |
| T-Mobile | Port Validation + Account PIN |
Call your provider and request:
-
A port-out PIN
-
A note on your account requiring in-person verification only
-
Restrictions against phone support making SIM or account changes
Also ask:
"Can you lock my SIM so it can't be moved to a new device without a store visit?"
📵 Step 3: Freeze Number Porting
Some carriers offer port freeze features that completely prevent transferring your number to another SIM unless you physically go to a retail store with ID.
This is critical. Without this lock:
-
Attackers can transfer your number online or via phone
-
Social engineering attacks succeed with only minimal PII
🔍 Where to Do It:
-
Verizon: MyVerizon app → "Number Lock"
-
T-Mobile: Call 611 and request Port Validation
Figure 2. Vulnerable vs Hardened Against SIM Swap. -
AT&T: Account Passcode + Extra Security flag
🔄 Step 4: Create a Second, Private Phone Number
Create a dedicated number only for high-security accounts:
-
Bank logins
-
Crypto platforms
-
Cloud storage
-
Email recovery
Never post this number publicly. Never link it to social profiles. Keep it air-gapped.
For everything else - social media, online forms, utilities - use a decoy public number.
🛰️ Step 5: Use Virtual Numbers or Offshore eSIMs
Hackers often target U.S. and EU-based numbers because they're tied to known carriers. Using secure VoIP or eSIM services adds another layer of difficulty.
Trusted Virtual Providers:
| Service | Security Benefits |
|---|---|
| MySudo | Multiple identities, VoIP with no carrier records |
| JMP.chat | Encrypted messaging via XMPP |
| SilentLink | Offshore, pseudonymous eSIM provider |
These services:
-
Don't store your identity in centralized databases
-
Aren't listed in mainstream carrier lookup tools
-
Make SIM swapping much harder (or impossible)
🔐 Step 6: Hardware Keys > Everything Else
Use FIDO2-compatible hardware keys like YubiKey or SoloKey for:
-
Gmail / Google Workspace
-
Microsoft accounts
-
GitHub
-
AWS and cloud portals
-
Password managers (1Password, Bitwarden)
They offer:
-
Phishing resistance
-
No codes to intercept
-
No recovery via phone number
"You can't SIM-swap a USB key." - Infosec Proverb
SMS is the lowest common denominator in account security - and SIM swaps weaponize that weakness.
By locking your carrier account, eliminating SMS authentication, and shifting to hardware-based MFA, you eliminate 95% of the attack surface.
Once attackers hijack your number, they rush to your inbox. That's because your email is the command center for everything you own. If they control it, they control you.
📧 Step 1: Secure Your Primary Email Accounts
If you're using Gmail, Outlook, or ProtonMail, lock them down like a vault.
🔐 Checklist for Email Protection:
| Control | Description |
|---|---|
| Unique strong password | Use a password manager like 1Password or Bitwarden |
| Hardware key (YubiKey) | Avoids phishing and SIM-based resets |
| Remove phone from recovery | SMS recovery = SIM swap vulnerability |
| Use recovery email, not number | Make it a secret account not used for anything else |
| Monitor logins | Set alerts for new device or IP activity |
| Backup codes | Store offline on paper or a secure USB stick |
Never use your phone number as a recovery option.
"Treat your email account as if it were your house keys, passport, and wallet rolled into one."
- Cybersecurity & Infrastructure Security Agency (CISA)
☁️ Step 2: Harden Cloud Storage & Productivity Platforms
Cloud accounts store sensitive business docs, personal info, and financial files - often synced from compromised mobile devices.
Protect Platforms Like:
-
Google Drive / Workspace
-
Dropbox
-
iCloud
-
Microsoft 365
Security Actions:
-
Enable MFA with app-based code or hardware token
-
Audit third-party apps with access
-
Revoke old devices and unused sessions
-
Review file-sharing settings: is your tax return shared with "Anyone with the link"?
👥 Step 3: Lock Down Social Media - Especially for Public Figures
Social media takeovers are used to:
-
Scam your followers (especially via crypto giveaways)
-
Damage your brand reputation
-
Leak personal photos or messages
-
Target family members
🔧 Platform-by-Platform Settings
| Platform | Key Defenses |
|---|---|
| Twitter/X | Use Security Key only; disable SMS 2FA entirely |
| 2FA app only; remove phone number; enable login alerts | |
| Review active sessions; enable hardware key or 2FA app | |
| Hide email and phone from public profile; monitor connection invites |
Pro Tip: Disable message requests from strangers where possible. Most SIM swap extortion and manipulation begins via direct messages.
Email and social accounts are usually the first stop after a SIM swap. Why? They unlock everything else.
Your defense must include:
-
Phone number removal
-
Strong MFA
-
Session and access hygiene
SIM swap attacks don't just steal money. They unravel your entire digital identity - and in the case of high-net-worth individuals, that damage ripples into your business, your reputation, your family, and your legacy.
Let's break down the full spectrum of damage with real-world cases and consequences.
💰 Financial Damage
This is the most immediate and obvious. But it's often underestimated.
🔻 Direct Losses
-
Bank wire transfers initiated using reset login + SMS
-
Crypto exchange account drained in minutes after takeover
-
PayPal / Venmo / Zelle abuse to send funds to mules
Figure 3. Hardening Your Phone Against SIM Swap. -
Unauthorized credit card charges or line-of-credit activations
"I lost $145,000 worth of ETH and USDC in less than 20 minutes. No notification until my Coinbase was locked."
- Anonymous victim via Reddit
🔻 Hidden Financial Risks
-
Opening loans or credit lines in your name
-
Filing fraudulent tax returns to intercept refunds
-
Selling your personal and financial data on the dark web
👨👩👧👦 Family & Personal Life Disruption
When you're targeted as a wealthy individual, your family becomes part of the blast radius.
| Threat Type | Impact |
|---|---|
| Social engineering | Calls/texts to family members pretending to be you |
| Doxxing | Home address, family names, children's schools exposed |
| Threatening messages | Hackers blackmailing with deepfakes or stolen data |
| Reputation attack | Posting private photos, fake messages from your accounts |
Even if no funds are lost, the psychological impact is immense - especially when children or elderly family members are dragged into the attack chain.
🕵️♂️ Identity Theft and Legal Risk
Because your phone number is often used in:
-
Government services login (e.g., tax portals, DMV)
-
Healthcare portals
-
Multi-party verification (banks, trusts, estates)
A compromised SIM can lead to:
-
Fake identity creation using your name
-
Claiming benefits or tax returns fraudulently
-
Opening shell companies in your name
-
Interfering with legal proceedings or financial deals
"I nearly missed a seven-figure deal because the attacker contacted my law firm pretending to delay the signing."
- HNWI client, via internal case study
📉 Reputational Damage & Business Fallout
The damage doesn't stop at your personal identity. If you run or represent a business, the attacker can:
-
Hijack your email to issue fake invoices to clients
-
Post embarrassing or illegal content on your company's social channels
-
Exfiltrate confidential company docs via cloud access
-
Use your name to get access to private Slack channels, Zoom meetings, or developer accounts
This can result in:
-
Breach notification requirements (if company data was involved)
-
Client churn from perceived negligence
-
Loss of investor trust and valuation impact
-
Regulatory exposure (e.g. GDPR or HIPAA violations)
⚠️ Timeline of an Escalated SIM Swap
| Time | Attacker Action |
|---|---|
| 0 mins | Calls your carrier, impersonates you |
| 5 mins | Phone signal dies, SIM ported |
| 10 mins | Gmail reset via SMS code |
| 12 mins | Coinbase reset via Gmail link |
| 14 mins | Funds transferred to crypto mixer |
| 20 mins | Instagram account hijacked, fake giveaway posted |
| 25 mins | WhatsApp messages to family asking for urgent money |
| 30 mins | Hacker deletes recovery access, changes all passwords |
A SIM swap is a gateway attack. It starts with a text message and ends with your entire life compromised - from your finances and family to your legal identity.
Without a hardened mobile and authentication strategy, you're one carrier rep away from disaster.
If you're serious about avoiding a SIM swap attack, you need a plan. This isn't just about setting up 2FA once - it's about rebuilding your digital identity architecture to assume attackers are watching.
Below is your ultimate prevention checklist, broken down by priority, with tools, actions, and frequency.
✅ Core Prevention Actions
| Action | Tool/Method | Frequency |
|---|---|---|
| Remove SMS-based 2FA | Replace with YubiKey/Authy | One-time |
| Lock mobile carrier account | Port freeze, PIN, in-person validation only | One-time |
| Use private number for sensitive use | VoIP or second SIM (JMP.chat, MySudo) | One-time |
| Remove phone from recovery options | Email, bank, cloud accounts | One-time |
| Set up hardware key MFA | YubiKey, SoloKey, OnlyKey | One-time |
| Encrypt devices and enable remote wipe | macOS FileVault, Android/iOS built-in | One-time |
| Monitor new device logins | Google, Apple, Microsoft settings | Continuous |
🔒 Advanced Protections for HNWIs
| Action | Description | Tools/Services |
|---|---|---|
| Segment digital identities | Different emails/numbers for social, financial, admin | ProtonMail, custom domains |
| Remove data from broker sites | Opt-out or use DeleteMe, Kanary, OneRep | deleteme.com |
| Monitor for breaches | Email, phone, and password exposure alerts | HaveIBeenPwned, BreachAlarm |
| Doxxing countermeasures | Limit personal posts, obscure family identifiers | Private social media |
| Hire a privacy consultant | Evaluate executive exposure and communication habits | Atlant Security 😉 |
🧠 Proactive Habits
| Routine | Why It Matters | Frequency |
|---|---|---|
| Rotate passwords for key accounts | Limits long-term attack windows | Every 6 months |
| Review app permissions | Remove unused integrations | Quarterly |
| Revoke old sessions | Stop backdoor access | Monthly |
| Re-test recovery options | Confirm they're secure and private | Twice a year |
| Simulate SIM swap (internally) | Practice response and alert chains | Annually |
📂 Sample Tools & Links
-
YubiKey - FIDO2 & phishing-resistant hardware keys
-
Authy - Secure app-based MFA with multi-device sync
-
SilentLink - Offshore eSIM with no ID required
-
ProtonMail - Secure email with 2FA and recovery lock
-
Bitwarden - Open-source password manager
-
JMP.chat - Encrypted, decentralized phone alternative
-
DeleteMe - Opt-out service for data broker scrubbing
-
HaveIBeenPwned - Check if your info is in a breach
🧠 Final Thoughts
SIM swaps aren't going away. As long as carriers allow over-the-phone changes and recovery processes rely on phone numbers, you're vulnerable.
But you don't have to be defenseless.
By rebuilding your digital setup around:
-
Hardware-based authentication
-
Carrier-level controls
-
Identity segmentation
-
Threat monitoring and simulation
…you dramatically reduce your attack surface - and make yourself an expensive, unattractive target.
"They only need to succeed once. Your job is to make that success as costly, slow, and painful as possible."
- Zero-Day Survival Manual
🛡️ Need Help Securing Your Digital Identity?
Atlant Security offers private executive protection audits, including:
-
SIM swap prevention and active threat testing
-
Crypto asset protection strategy
-
Social engineering resilience training
-
Secure identity and comms architecture
📞 Book a confidential session at atlantsecurity.com/contact
See also: Why Your SMB Needs a Part‑time CISO Today - Expert Oversight Without the Full‑Time Cost
Related services from Atlant Security: IT Security Audit, Virtual CISO, All Services. Book a discovery call to discuss your specific situation.

Alexander Sverdlov
Founder of Atlant Security. Author of 2 information security books, cybersecurity speaker at the largest cybersecurity conferences in Asia and a United Nations conference panelist. Former Microsoft security consulting team member, external cybersecurity consultant at the Emirates Nuclear Energy Corporation.