APT. Oh, how I love this term. It became the fashion among security vendors so much that they started including it in every single page of their marketing materials. Every single vendor out there will come to a sales meeting saying their appliance magically defends against “APTs”. Do they even know what that means?
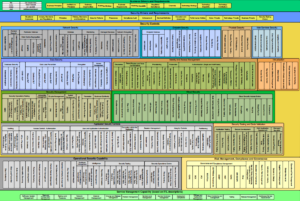
I would like to use an image to illustrate the idea:

Image credit: https://www.flickr.com/photos/soldiersmediacenter/8144569645
APT is not a ‘threat’ by itself. It is not the danger of being shot, it is the sniper, patiently waiting for your head to align with the crosshair of their sniper optics.
You can read the following book to thoroughly understand the meaning of it: Advanced Persistent Threat: Understanding the Danger and How to Protect Your Organization. I will just try to share my ideas below, to augment the rest of the content of my book with the term. After all, what good is a security book if it does not mention APTs?
No vendor can prevent APT
This is like saying that a band aid will prevent bullet wounds – when what you should really be focusing on is to avoid being in the way of a bullet in the first place, as in this analogy the APT is the shooter, not the bullet. No vendor or appliance can prevent motivated, well-funded and trained individuals from having an interest and motivation to attack you. What you can do though and what this book is about is to raise the adversary’s cost to attack you by focused, patient and persistent work on becoming an Advanced Persistent Defender.
APT is a bad term. I would say a better term is Advanced Persistent Attacker (or Advanced Persistent Adversary). Detecting them has become much more difficult because they (since 2008) no longer use files to store their backdoors on your systems – or at least avoid storing non-encrypted files.
You cannot detect apt activities with your AV nor can you spot their running code with a task manager. A good idea would be to dig into a memory dump from a suspicious machine – but are you going to do that continuously for all your machines?
What is left is network activity. But are you monitoring your power lines? Because APAs could be using your power lines to exfiltrate information – they will not (in many cases) use your networking equipment. Or they will install their own gateways inside your network and the traffic will never even touch your gateways.
Motivation is what drives them and while that motivation is backed by enough resources to justify pushing until a successful breach – and while the reward from that breach for them is bigger than the expense of pushing through your defenses – they will push.
Simple mathematics dictate that as long as your adversary’s resources and motivation are greater than your resources and motivation, they will prevail. That means one thing – use your resources wisely, stop spending humongous amounts of money on newer appliances and start thinking how to do more with less, as I am sure with proper configuration and hardening you can achieve more than if you buy and plug in all the security appliances on the market. Hopefully if you do your job in the best way possible you will raise the cost of breaching your defenses enough to deter as many adversaries as possible with the resources at hand.
In my opinion spending time and effort on proper configuration results in a higher security yield than spending money on products.
Being a persistent defender means creating invisible and difficult to penetrate data stores and user endpoints, hardening your servers and network devices according to military-grade best practices, controlling code and application execution, etc.
The process of creating a single well hardened desktop could take up months of your time – the benefits though will be quickly visible when you start deploying it across the enterprise.
It is faster and easier to buy somebody’s well sold promise, especially if it covers all your bases in terms of compliance to your favorite standards – but it has nothing to do with being a persistent defender and it will not help you keep your job when that promise fails to deliver.
Being an Advanced Persistent Defender is yet another animal and requires a never-ending process of reading and learning, as your adversaries never stop advancing their skills to the next level – just please don’t mistake learning with obtaining certifications. Can you imagine an advanced cyber attacker boasting a certificate as their skill to penetrate your defenses? Then why would you feel more capable to defend by being certified? As one of my very good friends pointed recently – a certificate is a beautiful packaging, nothing else. Make sure you pack a punch in that packaging or don’t go to the fight in the first place.
A bit part of being an APD is knowledge – that is why the next chapter will focus on obtaining the knowledge necessary to build a good foundation.